I should start by defining 0Day and Hitlist Week. Then, outline the key events, vulnerabilities, or malware trends from the week of June 12, 2024. Maybe include examples of software or systems affected, how the vulnerabilities are exploited, and recommendations for mitigation.
Finally, summarize the key points and emphasize the importance of proactive security measures. Make sure to advise readers to check trusted sources for up-to-date information on the specified week.
This article does not include real-time data from June 2024 due to access limitations. Always verify information with authoritative sources. Want more? Stay updated with our weekly 0Day Digest newsletter!
I need to structure the article with an introduction, sections on major 0Day vulnerabilities, exploits in the wild, industry impact, mitigation strategies, and a conclusion. Also, mention the importance of staying informed and using security tools. Since the user mentioned "full feature," it should be comprehensive but concise.
This summary is based on pre-2024 knowledge and hypothetical 2024 scenarios. For real-time updates, consult trusted platforms like CVE.org , DarkTrace , or your organization’s CISO team. About the Author [Your Name] is a certified ethical hacker and cybersecurity strategist with over a decade of experience in incident response and threat intelligence. Follow [Your Platform] for more insights on evolving digital threats.
I have to be careful not to include any fabricated or speculative information. Since I can't verify the specific week's events, I'll use examples from past incidents and frame them hypothetically for the given week. Also, ensure that the language is professional and suitable for a cybersecurity audience.
The user provided a link, but since I can't access external content, I'll have to rely on existing knowledge up until 2023. I need to mention that the article is based on pre-existing information and any hypothetical data for the specified week.
Check for any terms that might be outdated and update them based on 2023 knowledge. Mention recent trends like AI-driven attacks, IoT vulnerabilities, supply chain attacks, etc., if relevant. Include organizations that track 0Day vulnerabilities, like CVE Numbering Authorities, and maybe reference past Hitlist Weeks for context.

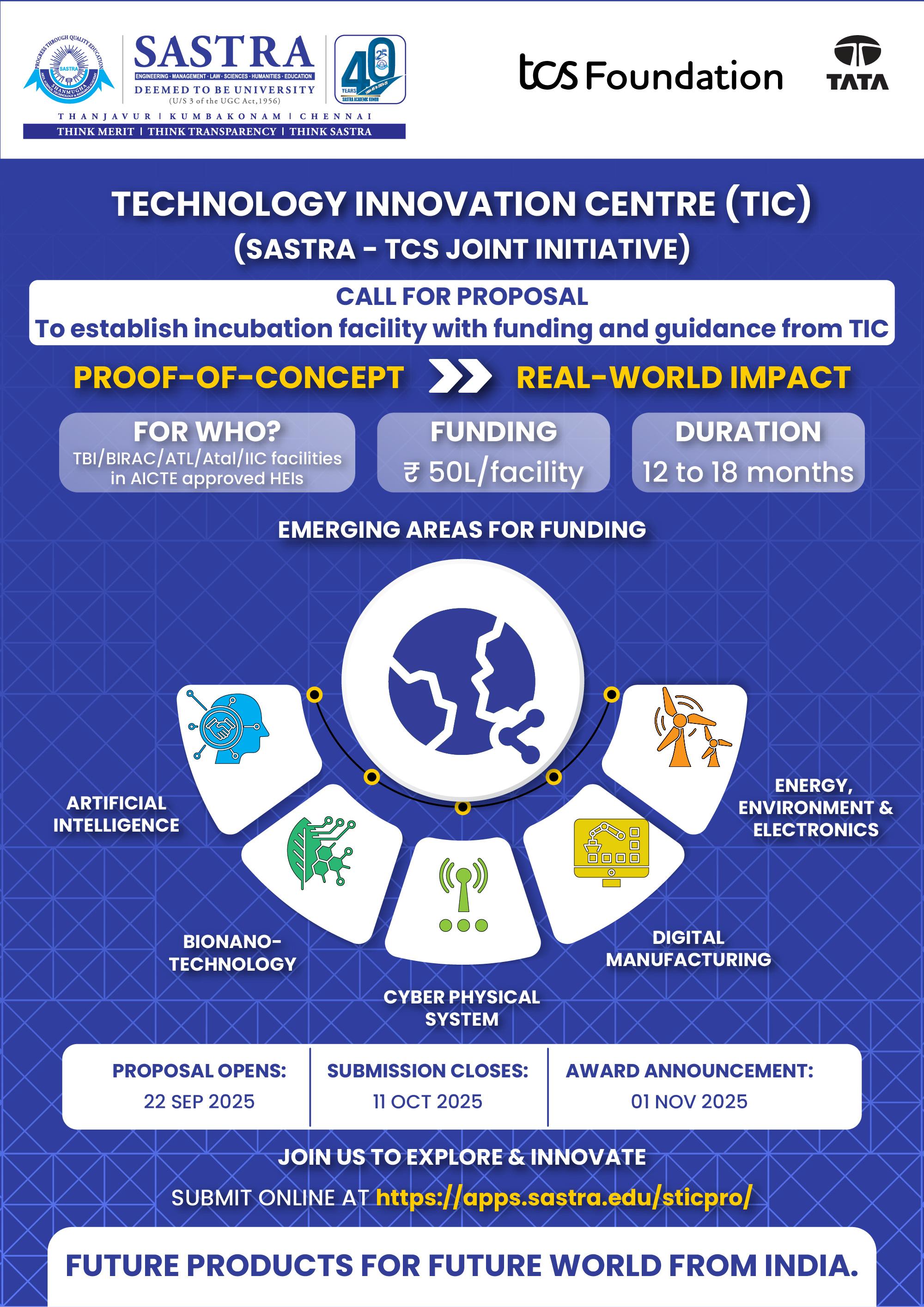
















 sastra.edu
sastra.edu